Navigating the Landscape of Enterprise Security: A Comprehensive Guide to the ESSEC Map
Related Articles: Navigating the Landscape of Enterprise Security: A Comprehensive Guide to the ESSEC Map
Introduction
With enthusiasm, let’s navigate through the intriguing topic related to Navigating the Landscape of Enterprise Security: A Comprehensive Guide to the ESSEC Map. Let’s weave interesting information and offer fresh perspectives to the readers.
Table of Content
Navigating the Landscape of Enterprise Security: A Comprehensive Guide to the ESSEC Map
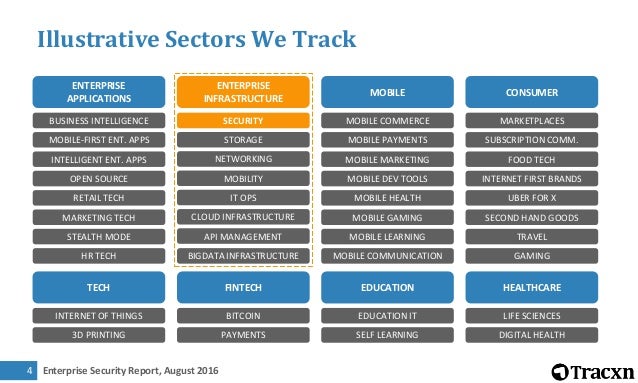
The ever-evolving threat landscape necessitates a robust and comprehensive approach to enterprise security. This is where the ESSEC Map, a framework for mapping and understanding the security posture of an organization, comes into play. This guide aims to provide a comprehensive understanding of the ESSEC Map, its benefits, and how it can be effectively implemented within an organization.
Understanding the ESSEC Map
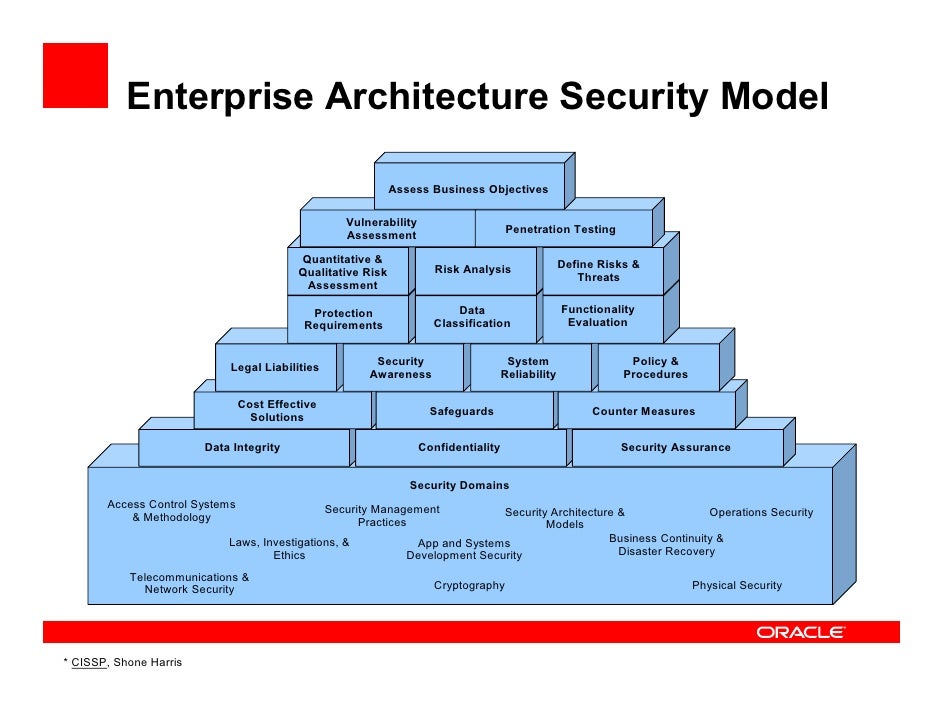
The ESSEC Map, an acronym for Enterprise Security Ecosystem and Control Map, is a visual representation of an organization’s security landscape. It serves as a valuable tool for understanding the interconnectedness of security controls, identifying potential vulnerabilities, and prioritizing security initiatives. This map, often presented as a flowchart or diagram, visually depicts:
- Assets: This includes all critical systems, data, and infrastructure that require protection.
- Threats: These are potential risks that could compromise the organization’s security, ranging from cyberattacks to internal threats.
- Vulnerabilities: These are weaknesses within the organization’s security posture that could be exploited by threats.
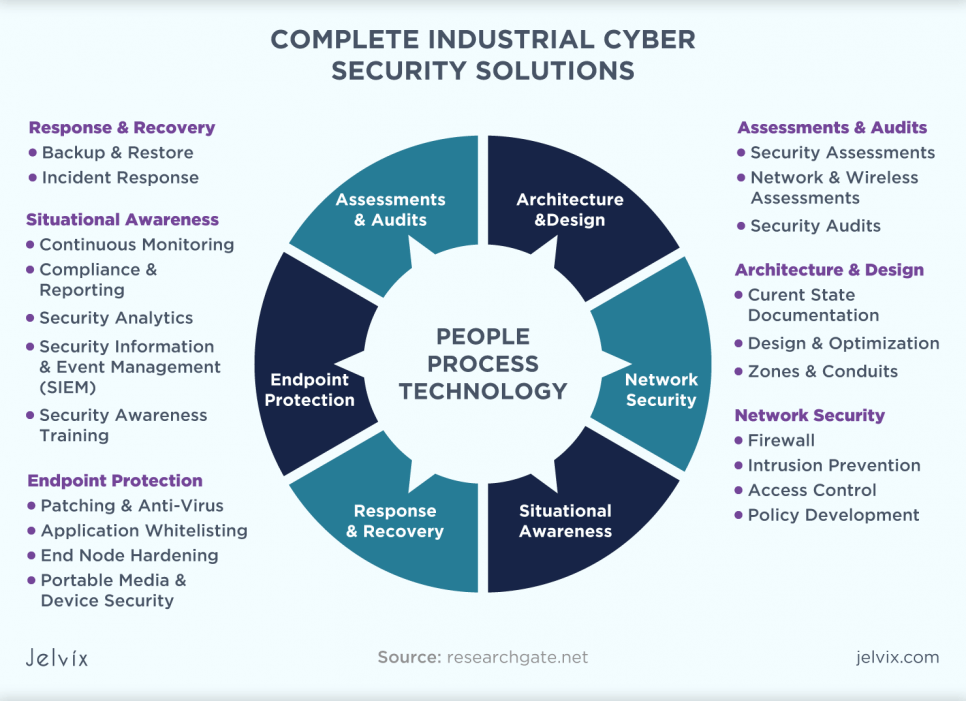
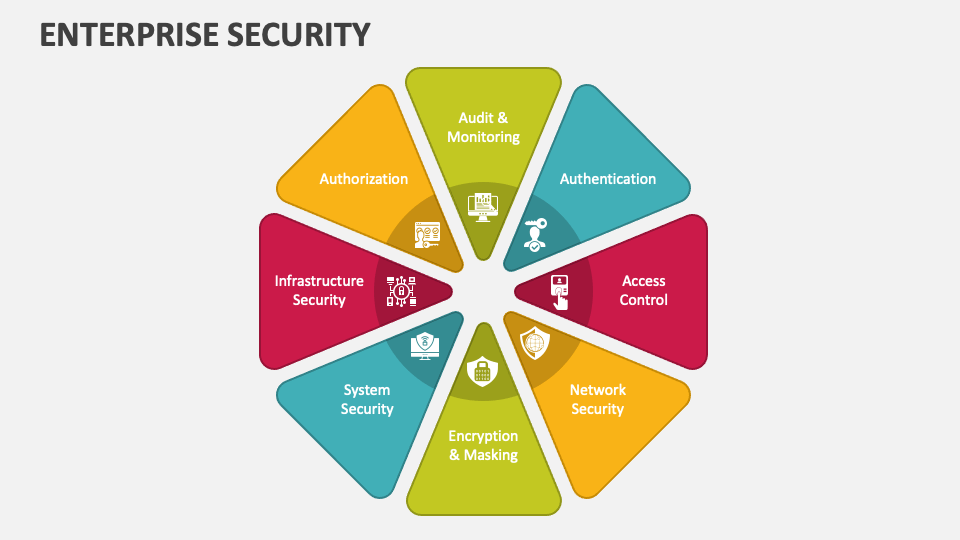
- Controls: These are safeguards implemented to mitigate threats and vulnerabilities, such as firewalls, intrusion detection systems, and security policies.
- Processes: These are the workflows and procedures used to manage security risks and implement controls.
Benefits of Utilizing the ESSEC Map
Implementing the ESSEC Map offers numerous benefits for organizations seeking to enhance their security posture. These benefits include:
- Improved Visibility: The map provides a holistic view of the organization’s security landscape, enabling a clear understanding of the interconnectedness of assets, threats, vulnerabilities, controls, and processes.
- Enhanced Risk Management: By identifying and analyzing potential threats and vulnerabilities, organizations can prioritize risk mitigation efforts and allocate resources effectively.
- Streamlined Security Operations: The map facilitates efficient communication and collaboration between security teams, ensuring alignment and consistency in security initiatives.
- Enhanced Compliance: The ESSEC Map helps organizations demonstrate compliance with relevant regulations and industry standards, reducing the risk of security breaches and legal repercussions.
- Improved Security Posture: By identifying gaps in security controls and implementing necessary measures, organizations can significantly enhance their overall security posture.
Building the ESSEC Map: A Step-by-Step Guide
Creating an effective ESSEC Map requires a systematic approach. Here’s a step-by-step guide:
- Define Scope and Objectives: Clearly define the scope of the map, including the specific assets, threats, and vulnerabilities to be included. Establish the objectives of the map, such as identifying critical vulnerabilities or improving risk management.
- Identify Assets: Conduct an inventory of all critical assets within the organization, including physical infrastructure, software applications, data, and intellectual property.
- Identify Threats: Analyze potential threats that could target the organization’s assets, considering both external and internal risks.
- Assess Vulnerabilities: Evaluate the organization’s security posture against identified threats, identifying potential weaknesses that could be exploited.
- Map Existing Controls: Document all existing security controls, including their purpose, effectiveness, and limitations.
- Define Processes: Map out the organization’s security processes, including incident response, vulnerability management, and security awareness training.
- Visualize the Map: Create a clear and concise visual representation of the ESSEC Map, using flowcharts, diagrams, or other appropriate tools.
- Regularly Review and Update: The ESSEC Map is a living document and should be regularly reviewed and updated to reflect changes in the organization’s security landscape, threats, and vulnerabilities.
FAQs about the ESSEC Map
Q: What is the difference between the ESSEC Map and a Security Control Framework?
A: While both address security management, the ESSEC Map is a visual representation of the organization’s security landscape, providing a comprehensive overview. Security control frameworks, such as NIST CSF or ISO 27001, offer a structured approach to implementing and managing security controls. The ESSEC Map can be used to visualize and understand the implementation of specific security controls within a framework.
Q: How can the ESSEC Map be used to prioritize security initiatives?
A: By analyzing the map, organizations can identify high-risk assets and vulnerabilities. This information can be used to prioritize security initiatives, focusing on areas that pose the greatest risk to the organization.
Q: Is the ESSEC Map suitable for all organizations?
A: The ESSEC Map can be tailored to fit the specific needs of any organization, regardless of size or industry. However, the complexity of the map may need to be adjusted based on the organization’s security maturity and the level of detail required.
Tips for Effective ESSEC Map Implementation
- Engage Key Stakeholders: Involve relevant stakeholders from across the organization, including IT, security, and business units, in the development and implementation of the ESSEC Map.
- Use Clear and Concise Language: Ensure the map is easily understandable by all stakeholders, using clear and concise language and avoiding technical jargon.
- Regularly Review and Update: The ESSEC Map should be reviewed and updated regularly to reflect changes in the organization’s security landscape, threats, and vulnerabilities.
- Utilize Technology: Consider using security assessment tools and vulnerability scanners to automate the process of identifying vulnerabilities and mapping controls.
- Promote Security Awareness: Use the ESSEC Map to educate employees about the organization’s security posture and their role in maintaining security.
Conclusion
The ESSEC Map is a powerful tool for organizations seeking to enhance their security posture and mitigate risks. By providing a clear and comprehensive view of the organization’s security landscape, the ESSEC Map enables organizations to make informed decisions about security investments, prioritize risk mitigation efforts, and improve overall security awareness. Through effective implementation and ongoing maintenance, the ESSEC Map can serve as a valuable asset for organizations seeking to navigate the ever-evolving threat landscape.





Closure
Thus, we hope this article has provided valuable insights into Navigating the Landscape of Enterprise Security: A Comprehensive Guide to the ESSEC Map. We thank you for taking the time to read this article. See you in our next article!